1
/
of
12
www.ChineseStandard.us -- Field Test Asia Pte. Ltd.
GM/T 0050-2016 English PDF (GM/T0050-2016)
GM/T 0050-2016 English PDF (GM/T0050-2016)
Regular price
$170.00
Regular price
Sale price
$170.00
Unit price
/
per
Shipping calculated at checkout.
Couldn't load pickup availability
GM/T 0050-2016: Cryptography Device Management - Specification of Device Management Technology
Delivery: 9 seconds. Download (and Email) true-PDF + Invoice.Get Quotation: Click GM/T 0050-2016 (Self-service in 1-minute)
Newer / historical versions: GM/T 0050-2016
Preview True-PDF
Scope
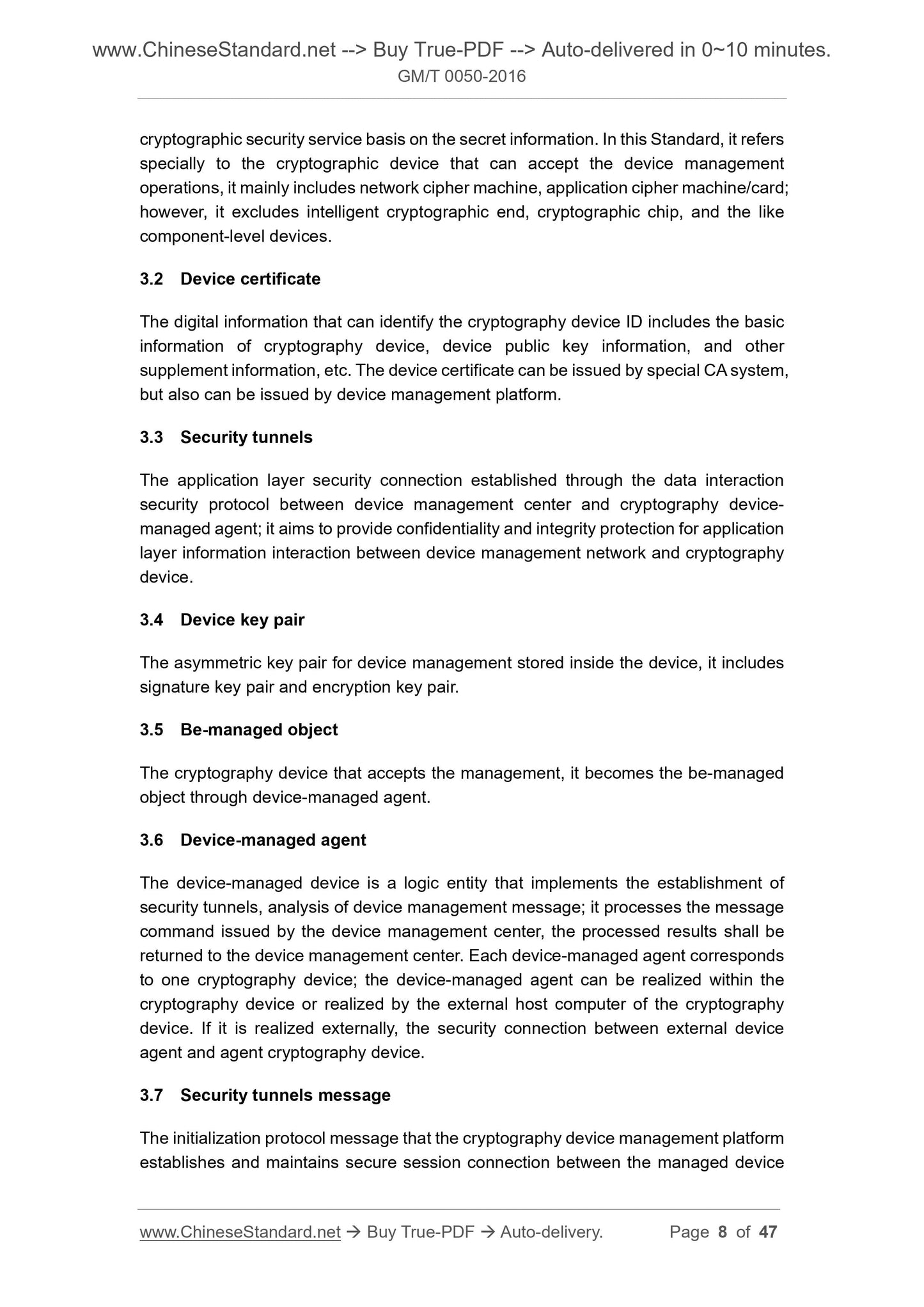
This Standard specifies the system structure, management process, security tunnelprotocol, management information structure, application interface and standard
management message format of cryptographic device management.
Provide guidance and basis for the study and development of cryptographic device
within the technical system framework and the upper management application.
This Standard is applicable to the study and development of cryptographic device
management system, cryptographic device management application, cryptographic
machine, and the like cryptographic devices; it can also be used for guiding the
inspection of cryptographic device management system and cryptographic device.
Basic Data
| Standard ID | GM/T 0050-2016 (GM/T0050-2016) |
| Description (Translated English) | Cryptography Device Management - Specification of Device Management Technology |
| Sector / Industry | Chinese Industry Standard (Recommended) |
| Classification of Chinese Standard | L80 |
| Word Count Estimation | 33,374 |
| Date of Issue | 2016-12-23 |
| Date of Implementation | 2016-12-23 |
| Regulation (derived from) | State Password Administration Notice No.31 |
| Issuing agency(ies) | State Administration of Cryptography |
Share