1
/
of
12
www.ChineseStandard.us -- Field Test Asia Pte. Ltd.
GM/T 0042-2015 English PDF (GM/T0042-2015)
GM/T 0042-2015 English PDF (GM/T0042-2015)
Regular price
$560.00
Regular price
Sale price
$560.00
Unit price
/
per
Shipping calculated at checkout.
Couldn't load pickup availability
GM/T 0042-2015: Test specification for cryptography and security protocol in tri-element peer architecture
Delivery: 9 seconds. Download (and Email) true-PDF + Invoice.Get Quotation: Click GM/T 0042-2015 (Self-service in 1-minute)
Newer / historical versions: GM/T 0042-2015
Preview True-PDF
Scope
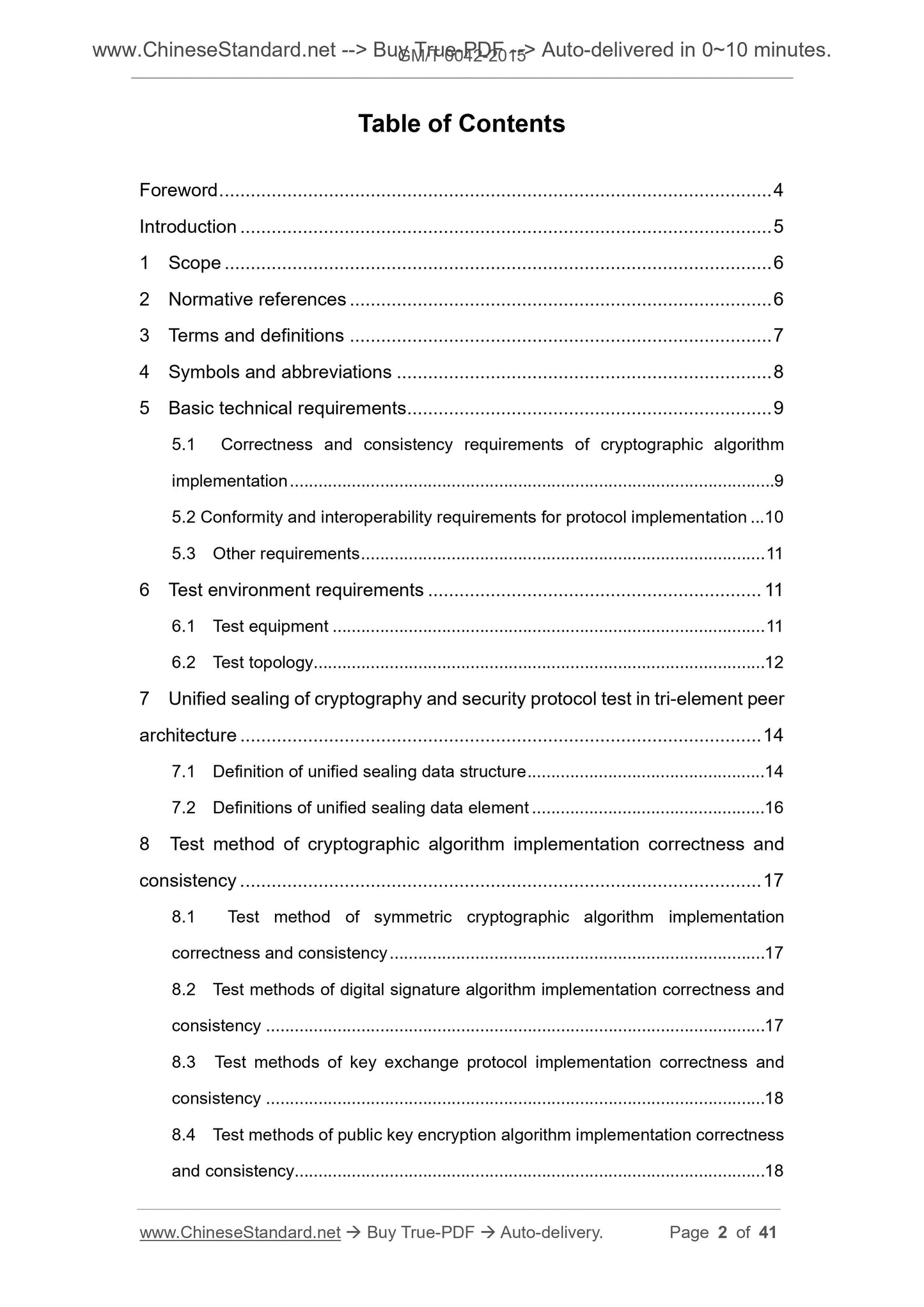
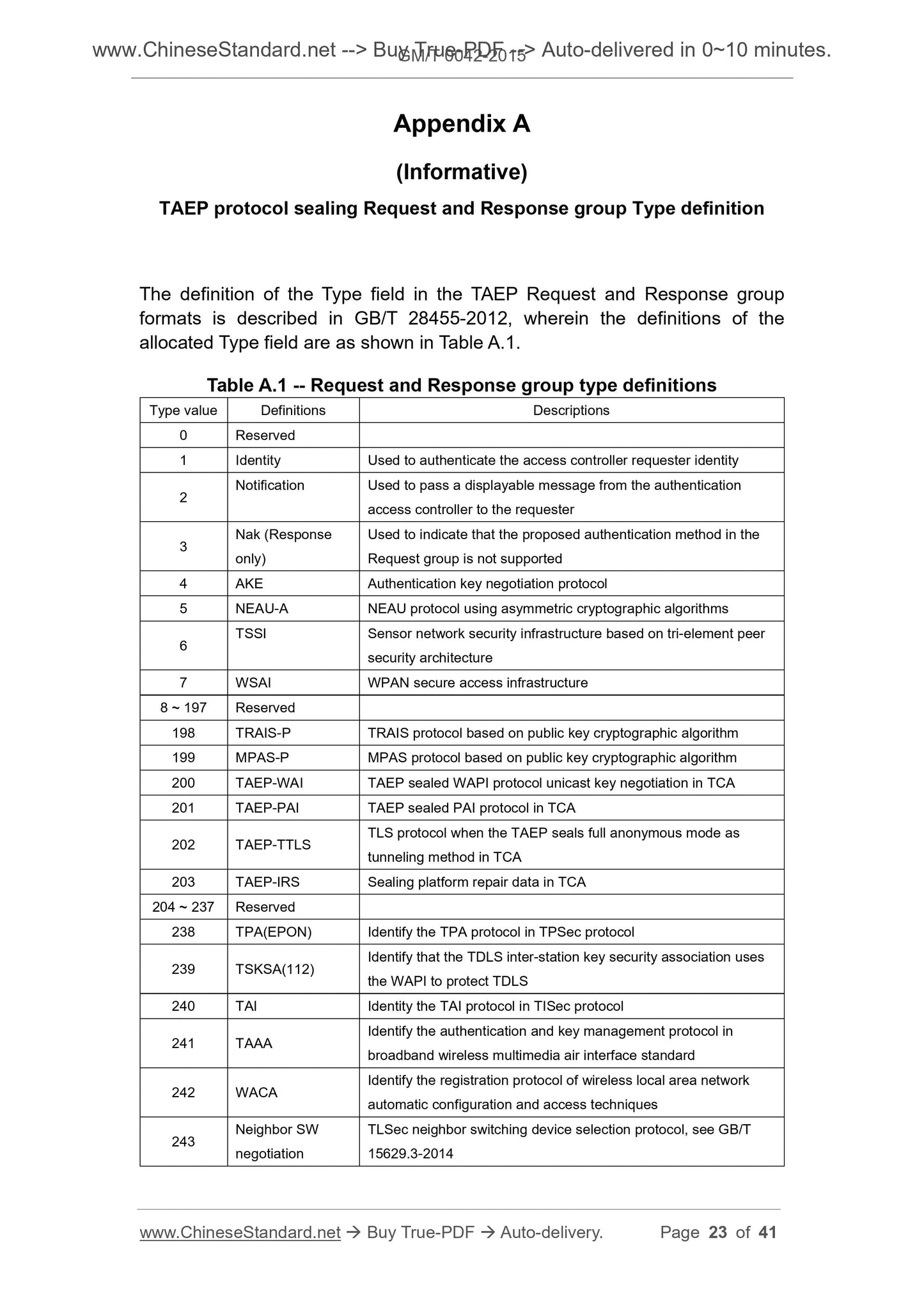
This standard specifies the basic technical requirements of the tri-element peerarchitecture cryptography security protocol for the relevant cryptography
algorithm and security protocol as well as the corresponding test methods, it is
applicable to the detection of tri-element peer cryptography security protocol-
related products. It mainly includes the following contents.
a) Technical requirements and test methods for the correctness and
consistency of cryptography algorithm implementation;
b) Basic technical requirements and test methods for compliance and
interoperability of the protocol implementation.
This standard applies to the equipment complying with ISO/IEC 9798-
3.1998/Amd.1.2010, GB/T 15843.3, GB/T 28455-2012, it is used to detect
whether its cryptography algorithm and protocol implementation comply with
the requirements of the above standards.
Basic Data
| Standard ID | GM/T 0042-2015 (GM/T0042-2015) |
| Description (Translated English) | Test specification for cryptography and security protocol in tri-element peer architecture |
| Sector / Industry | Chinese Industry Standard (Recommended) |
| Classification of Chinese Standard | L80 |
| Word Count Estimation | 27,240 |
| Issuing agency(ies) | State Administration of Cryptography |
Share