1
/
of
6
www.ChineseStandard.us -- Field Test Asia Pte. Ltd.
GM/T 0001.1-2012 English PDF (GM/T0001.1-2012)
GM/T 0001.1-2012 English PDF (GM/T0001.1-2012)
Regular price
$150.00
Regular price
Sale price
$150.00
Unit price
/
per
Shipping calculated at checkout.
Couldn't load pickup availability
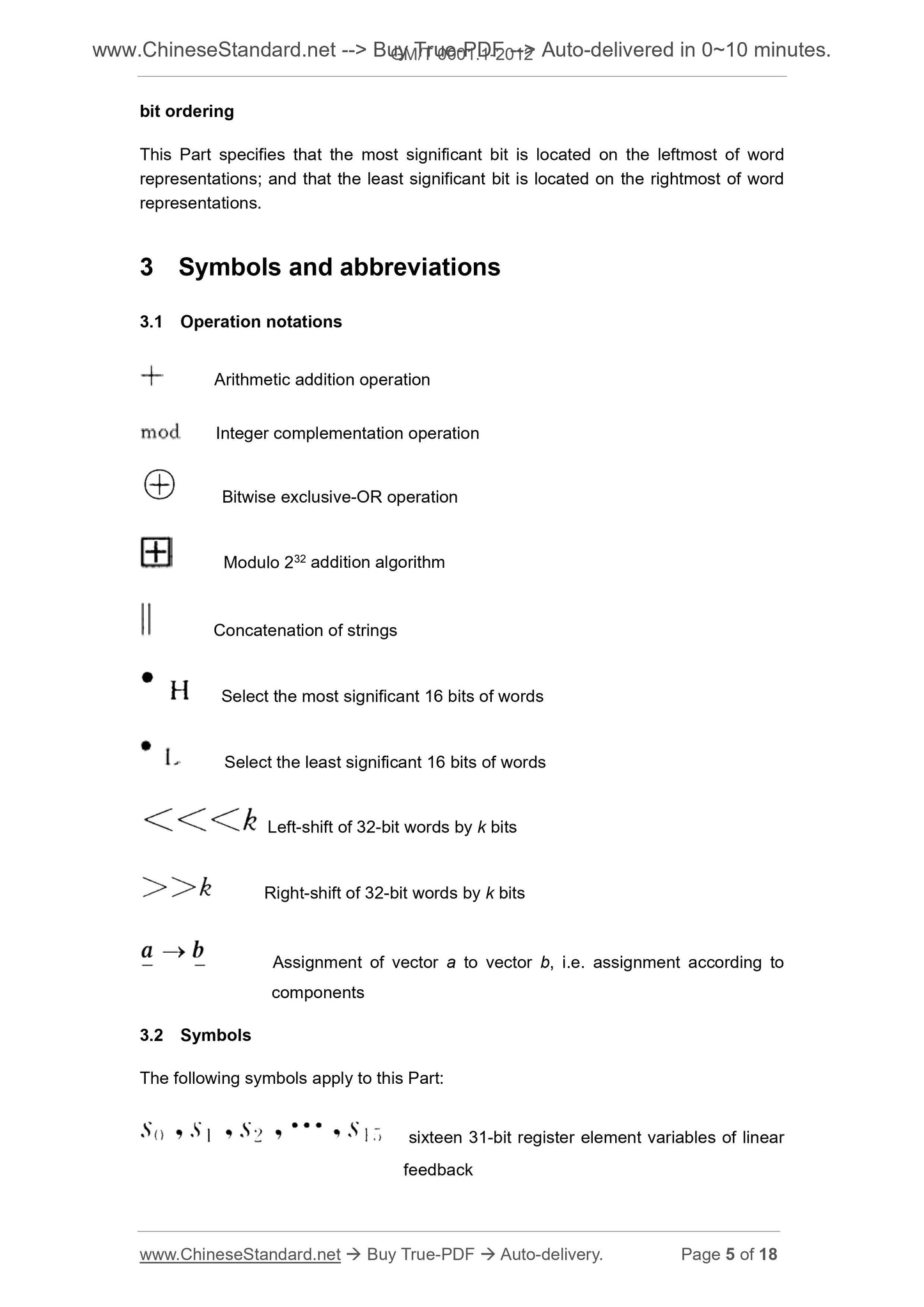
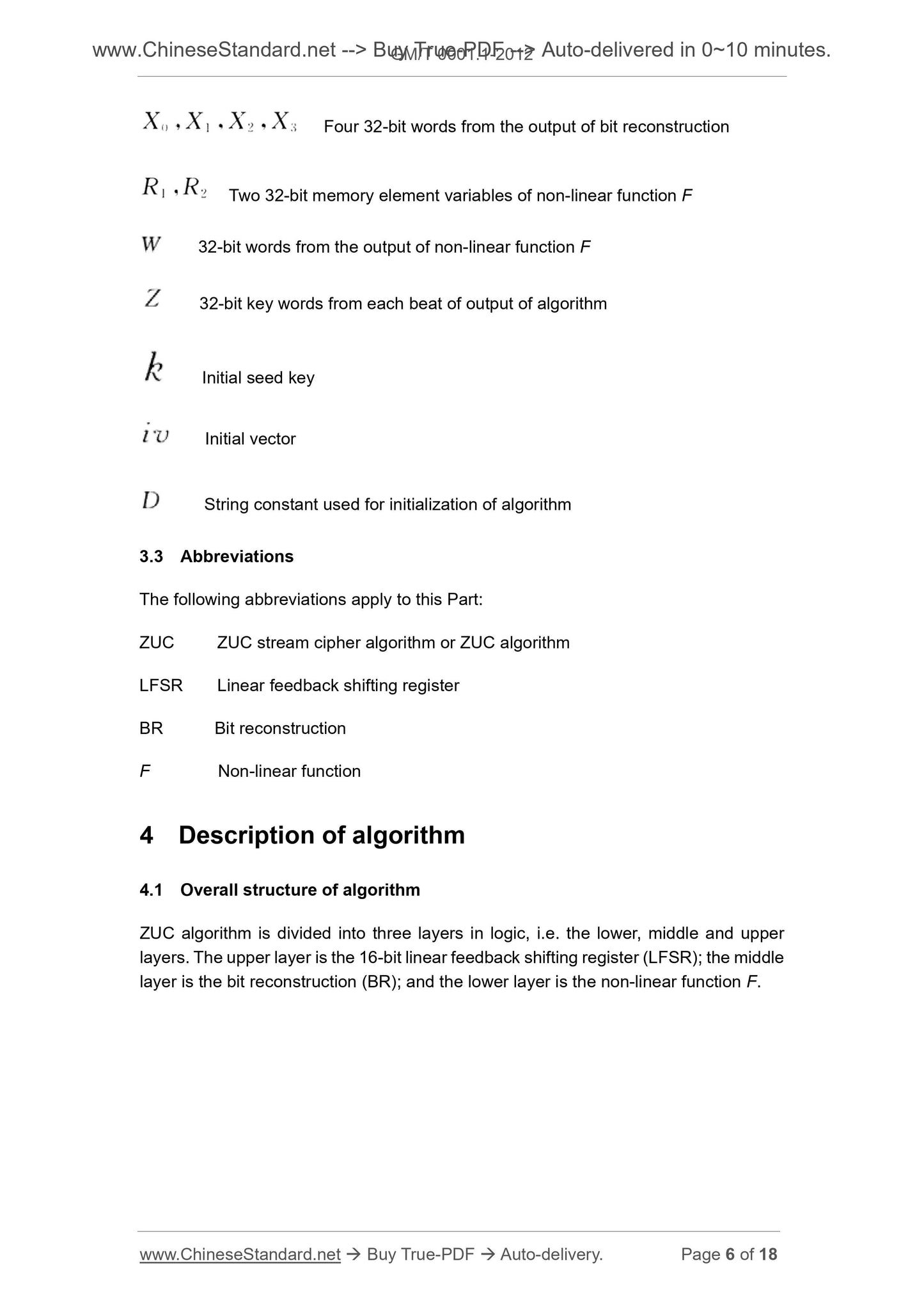
GM/T 0001.1-2012: ZUC stream cipher algorithm - Part 1: Description of the algorithm
Delivery: 9 seconds. Download (and Email) true-PDF + Invoice.Get Quotation: Click GM/T 0001.1-2012 (Self-service in 1-minute)
Newer / historical versions: GM/T 0001.1-2012
Preview True-PDF
Scope
This Part of GM/T 0001 describes ZUC stream cipher algorithm, which can be used asguidance for the development, testing and use of ZUC stream cipher algorithm related
products.
Basic Data
| Standard ID | GM/T 0001.1-2012 (GM/T0001.1-2012) |
| Description (Translated English) | ZUC stream cipher algorithm - Part 1: Description of the algorithm |
| Sector / Industry | Chinese Industry Standard (Recommended) |
| Classification of Chinese Standard | L80 |
| Word Count Estimation | 17,192 |
| Date of Issue | 3/21/2012 |
| Date of Implementation | 3/21/2012 |
| Issuing agency(ies) | State Administration of Cryptography |
Share