1
/
of
9
www.ChineseStandard.us -- Field Test Asia Pte. Ltd.
GB/T 37373-2019 English PDF (GB/T37373-2019)
GB/T 37373-2019 English PDF (GB/T37373-2019)
Regular price
$150.00
Regular price
Sale price
$150.00
Unit price
/
per
Shipping calculated at checkout.
Couldn't load pickup availability
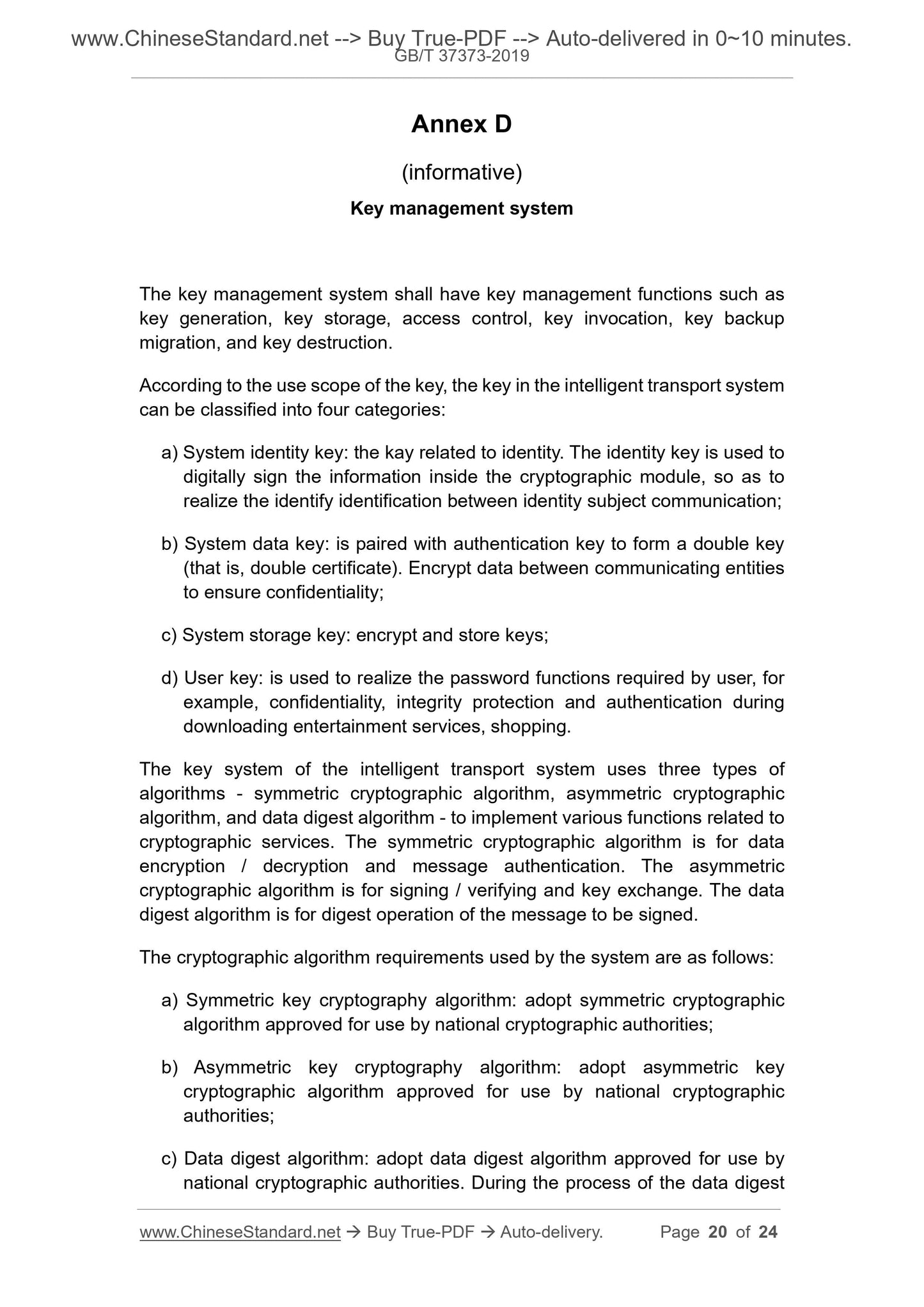
GB/T 37373-2019: Intelligent transport - Data security service
Delivery: 9 seconds. Download (and Email) true-PDF + Invoice.Get Quotation: Click GB/T 37373-2019 (Self-service in 1-minute)
Newer / historical versions: GB/T 37373-2019
Preview True-PDF
Scope
This Standard specifies security support platform and data security service ofintelligent transport system.
This Standard is applicable to intelligent transport system to realize data
security service that is based on cryptography.
Basic Data
| Standard ID | GB/T 37373-2019 (GB/T37373-2019) |
| Description (Translated English) | Intelligent transport - Data security service |
| Sector / Industry | National Standard (Recommended) |
| Classification of Chinese Standard | R85 |
| Classification of International Standard | 03.220.20 |
| Word Count Estimation | 18,167 |
| Date of Issue | 2019-05-10 |
| Date of Implementation | 2019-12-01 |
| Issuing agency(ies) | State Administration for Market Regulation, China National Standardization Administration |
Share