1
/
of
12
www.ChineseStandard.us -- Field Test Asia Pte. Ltd.
GB/T 31915-2015 English PDF (GB/T31915-2015)
GB/T 31915-2015 English PDF (GB/T31915-2015)
Regular price
$310.00
Regular price
Sale price
$310.00
Unit price
/
per
Shipping calculated at checkout.
Couldn't load pickup availability
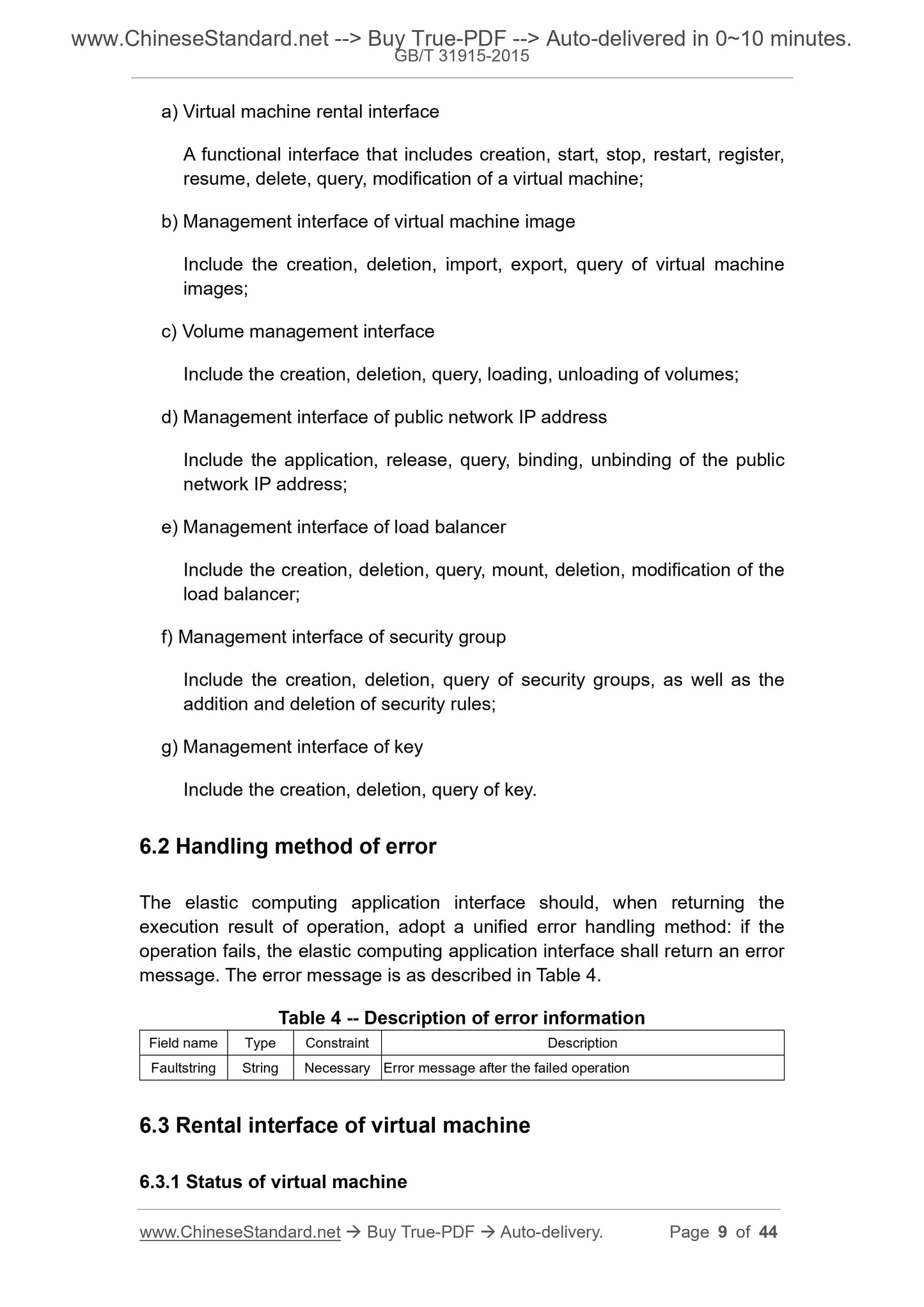
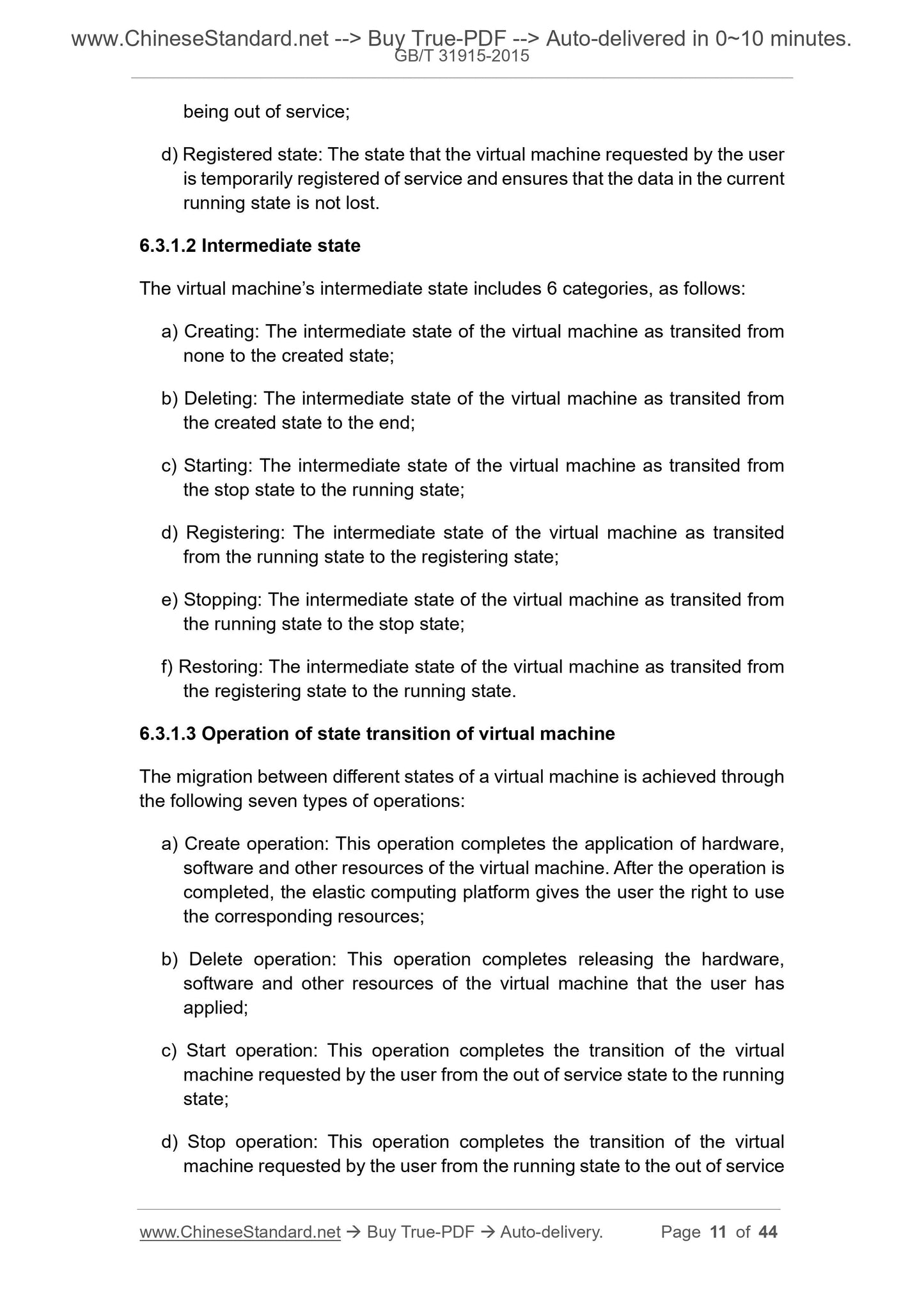
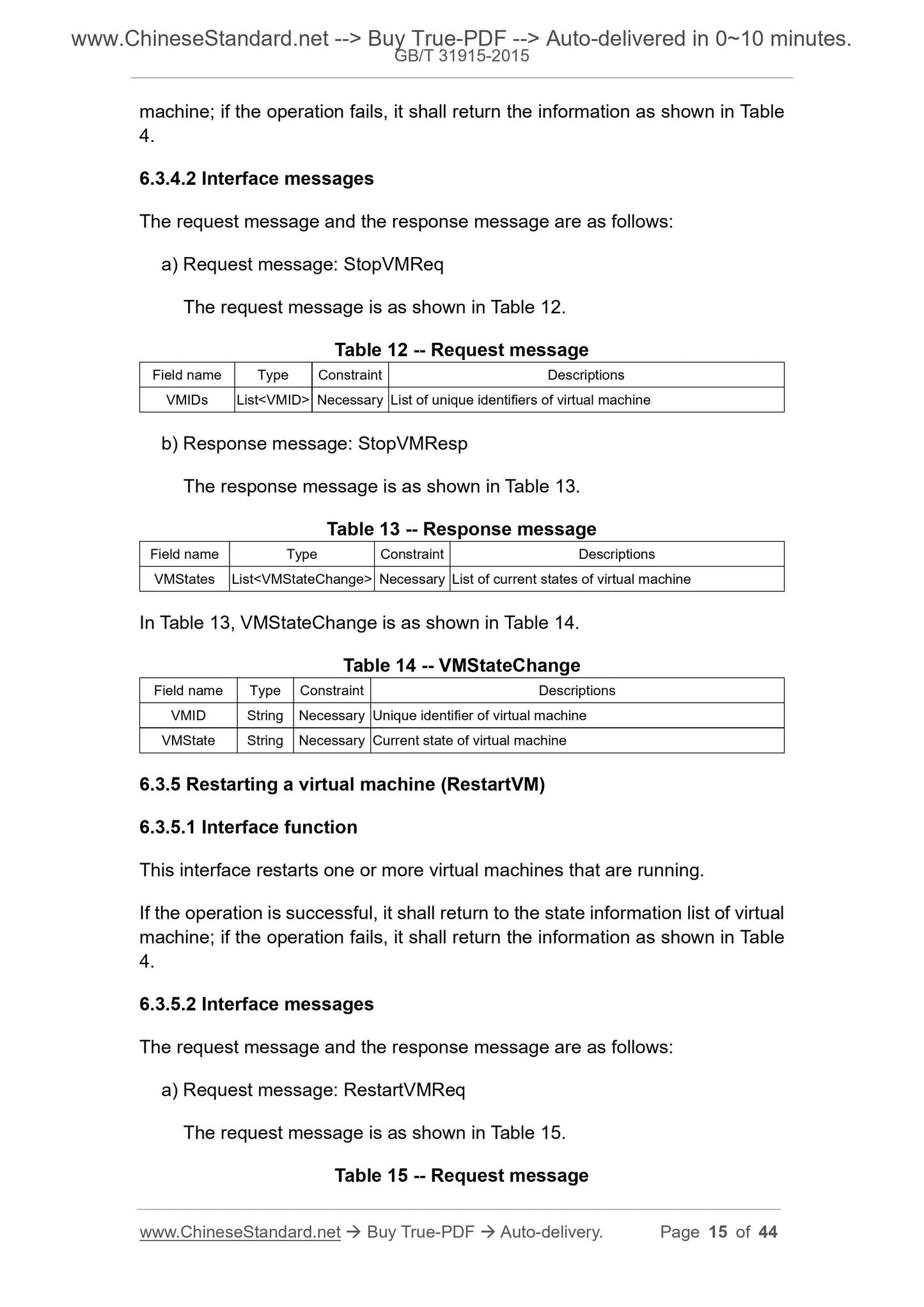
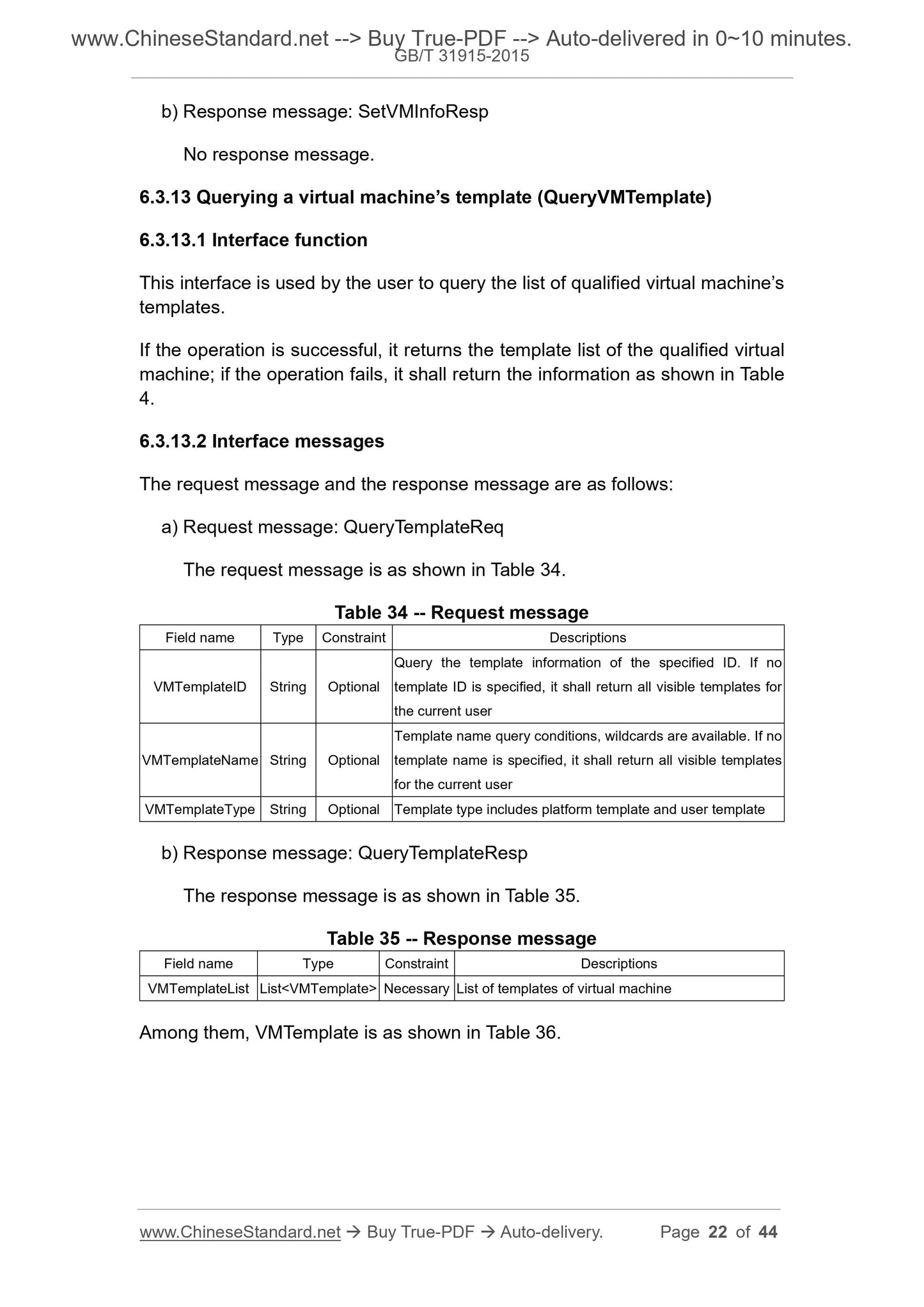
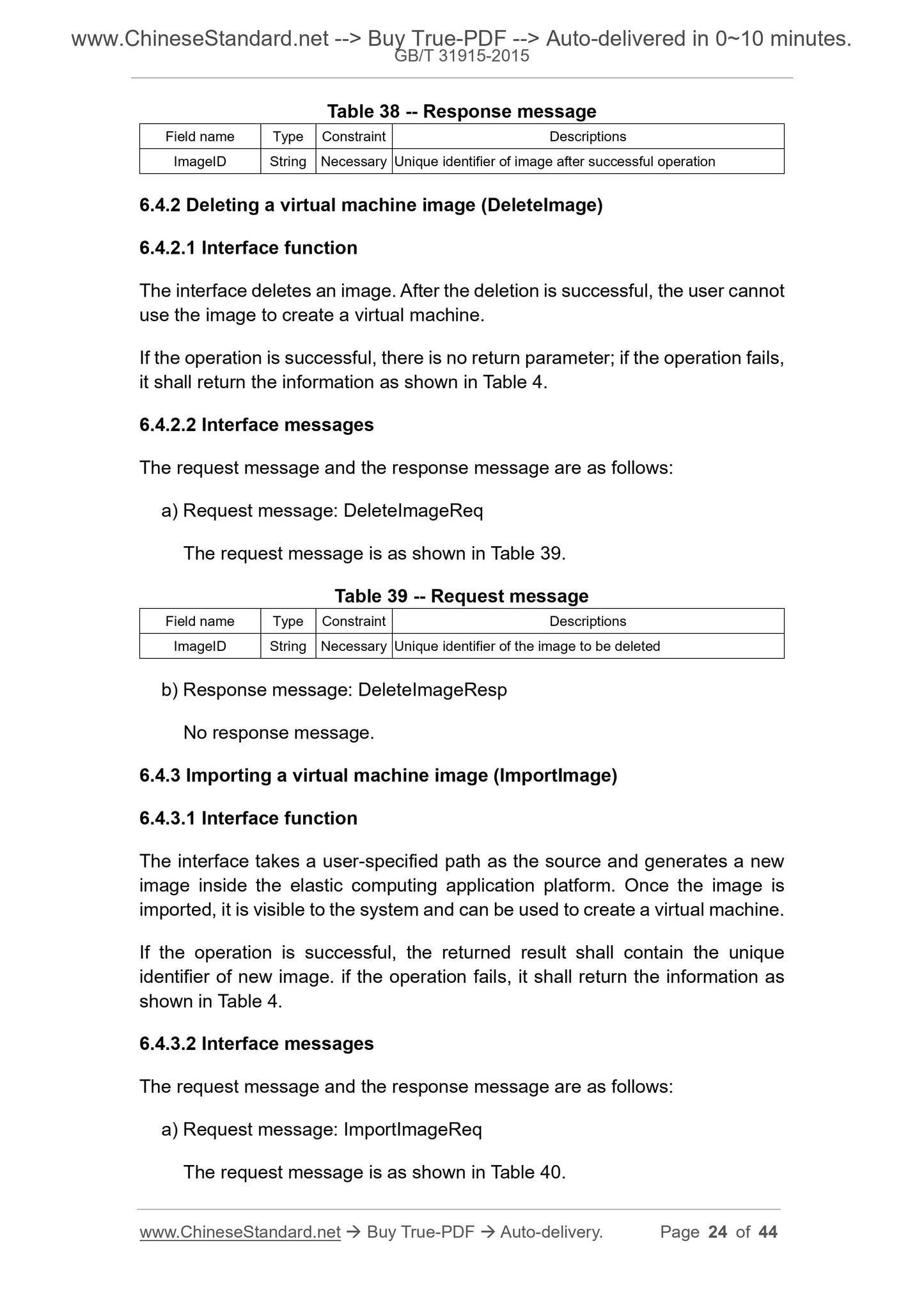
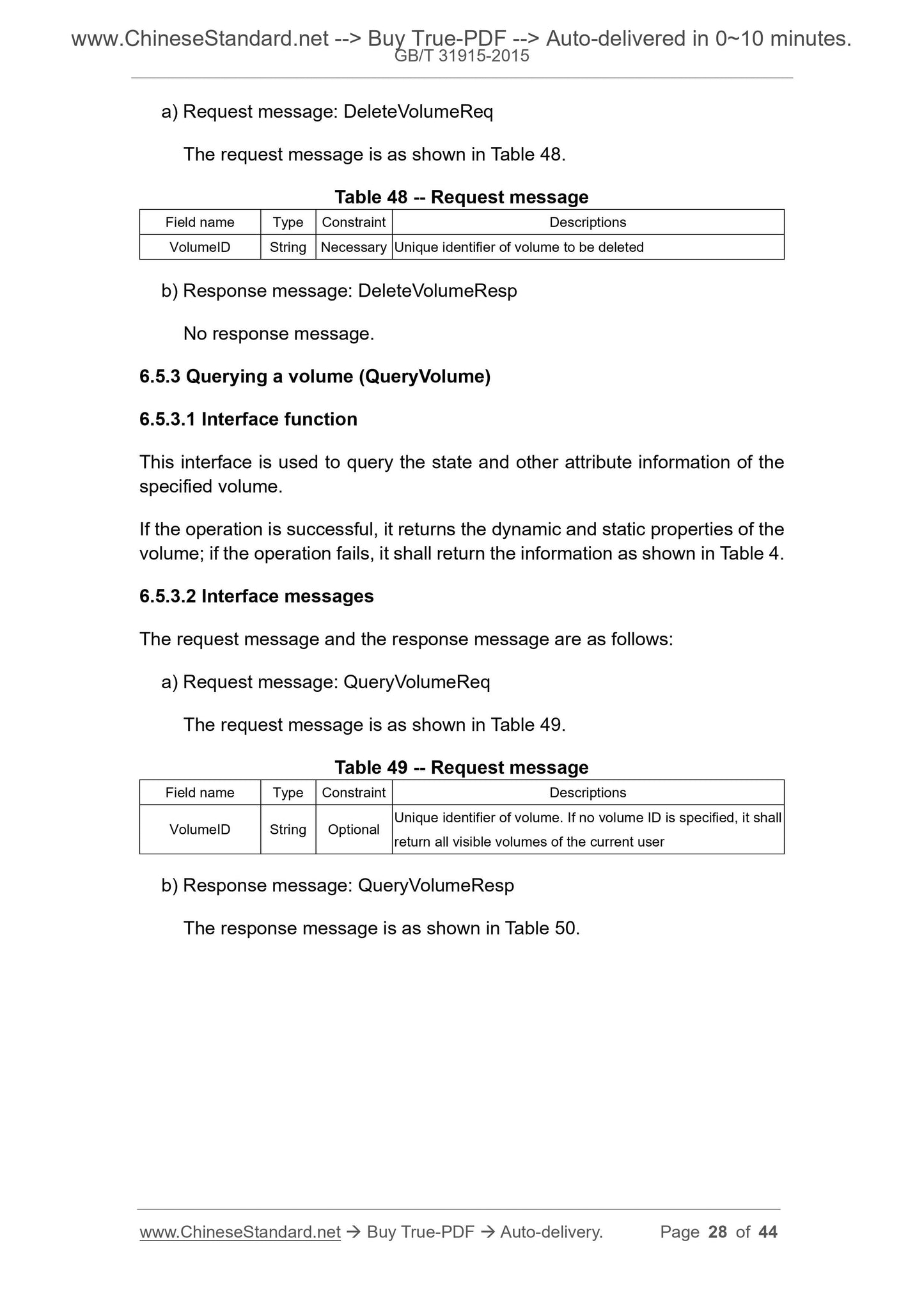
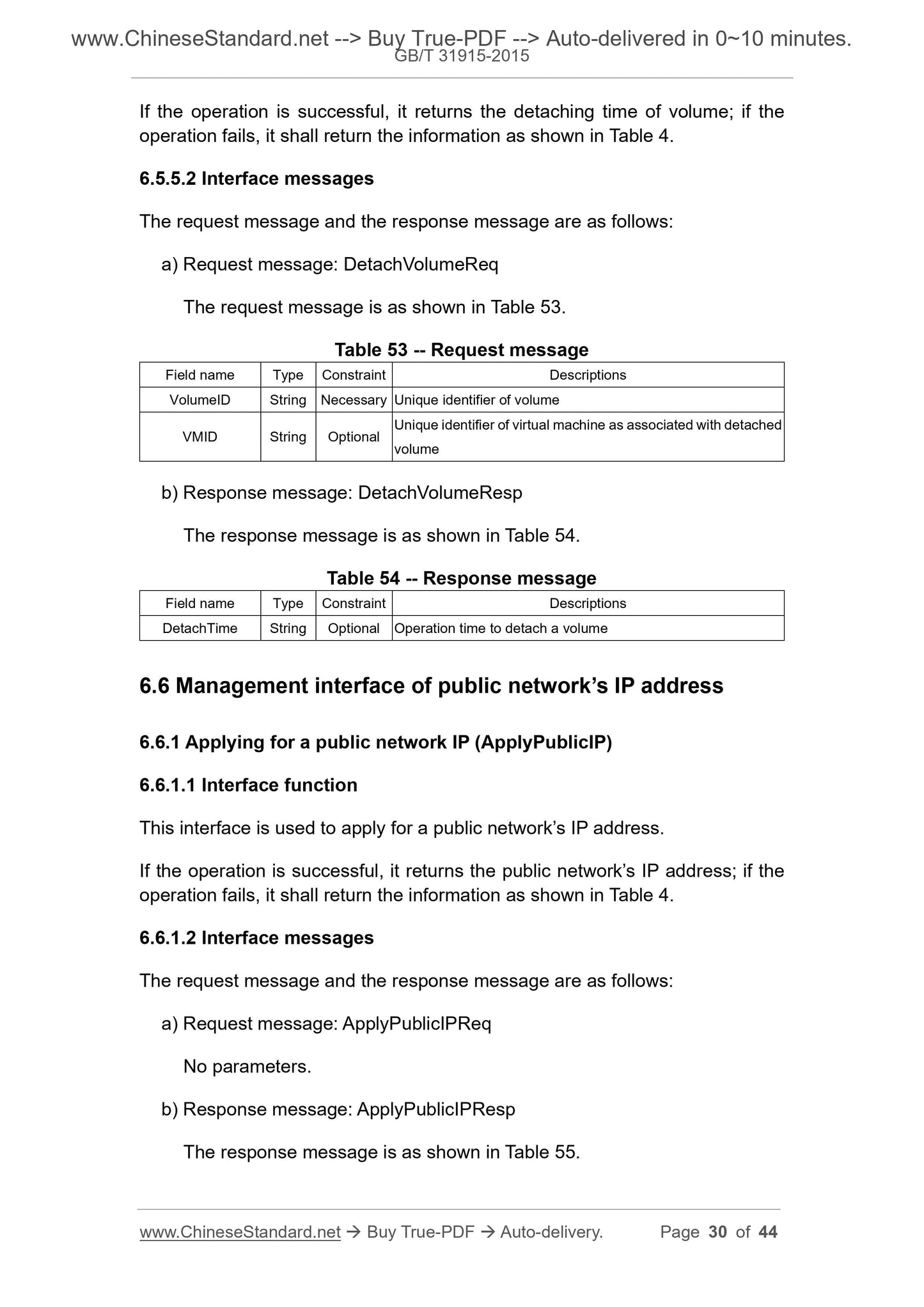
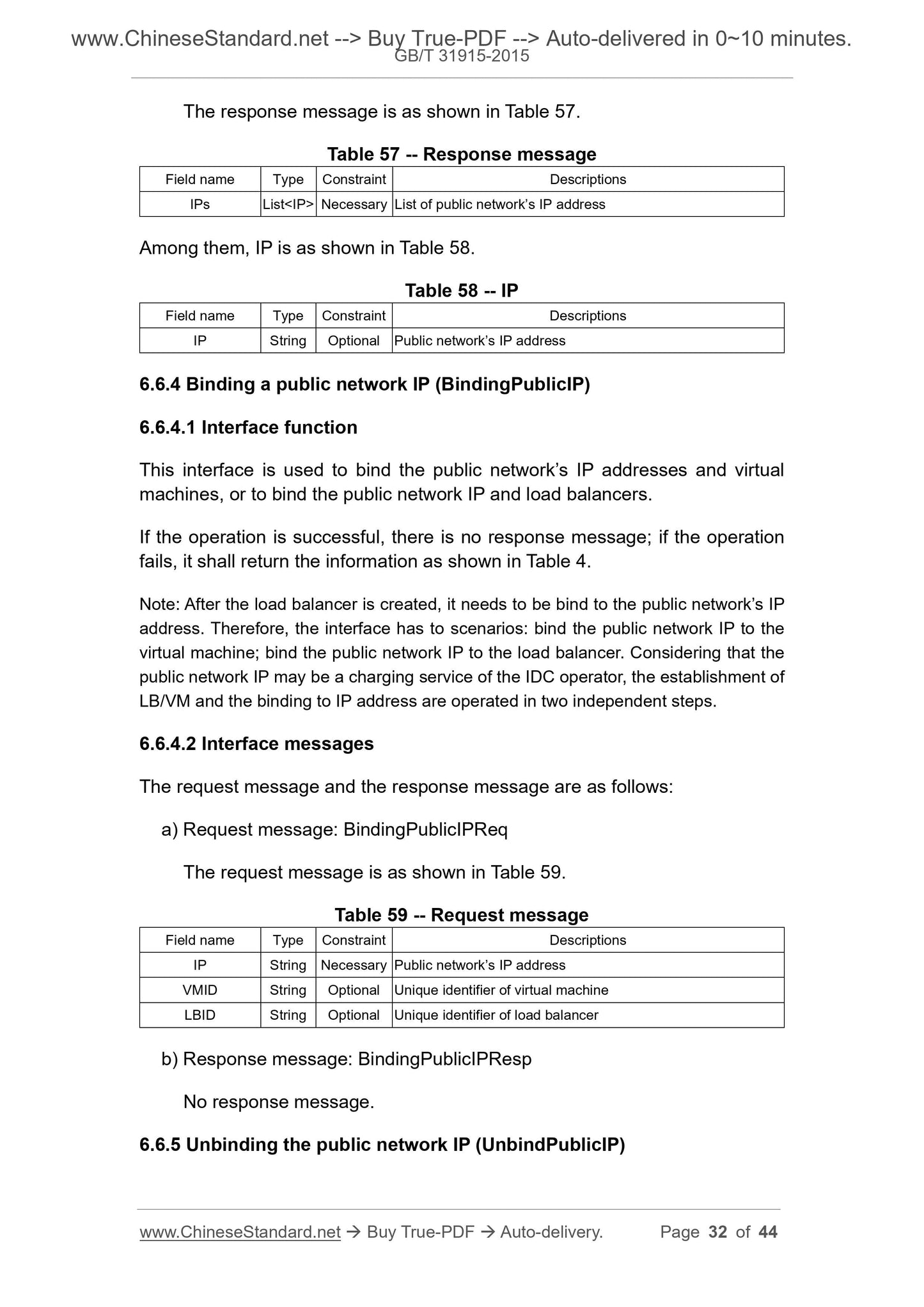
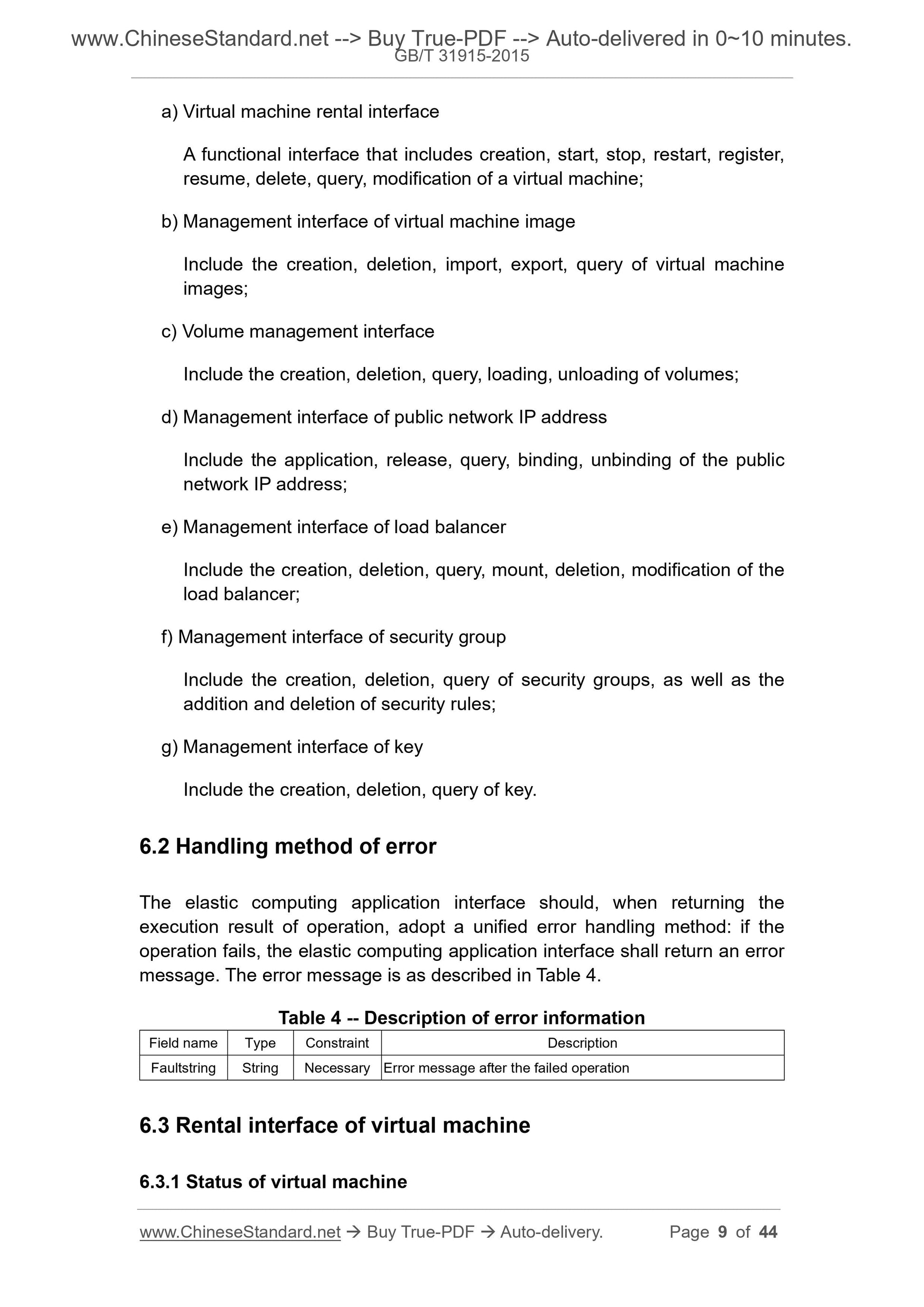
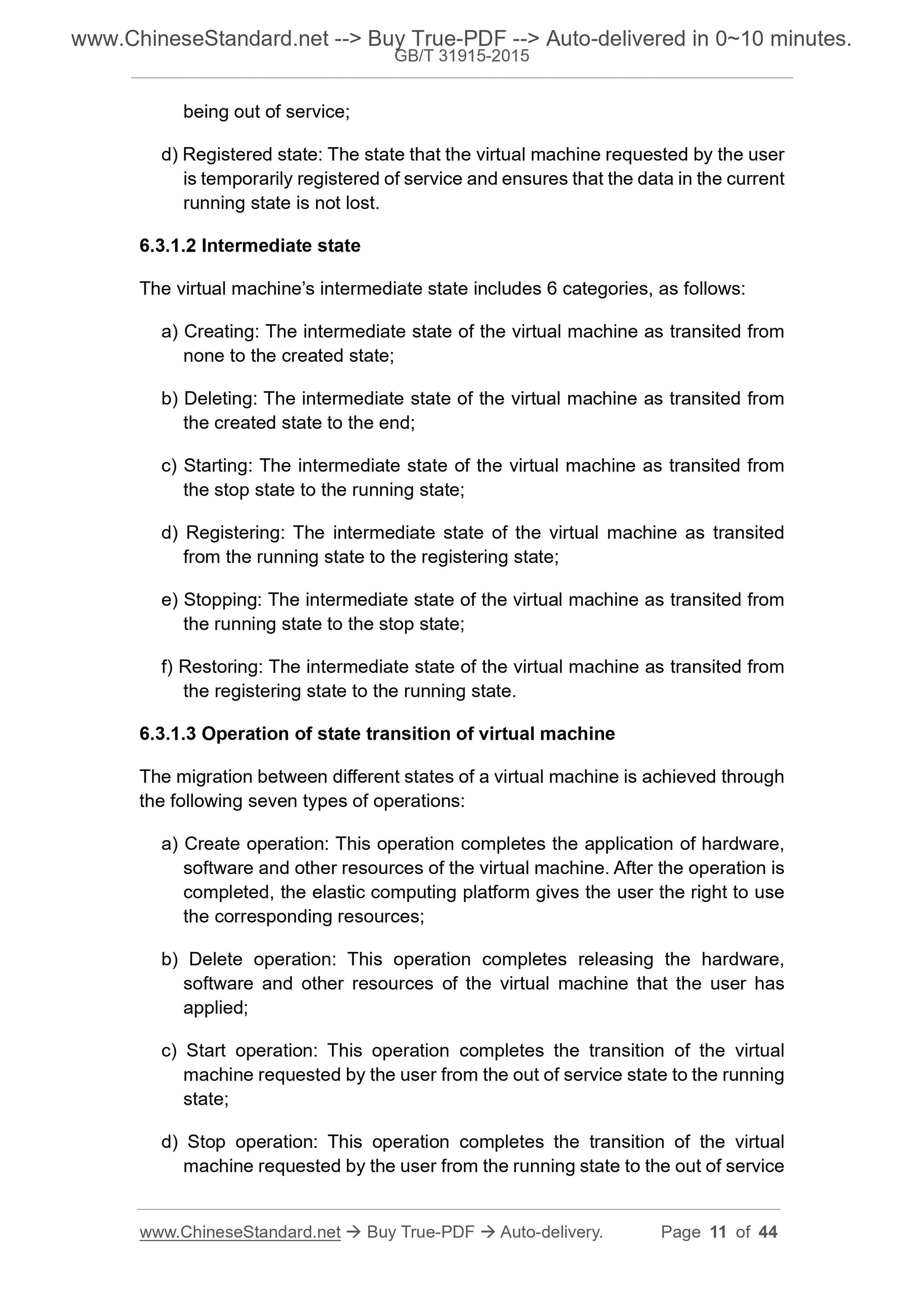
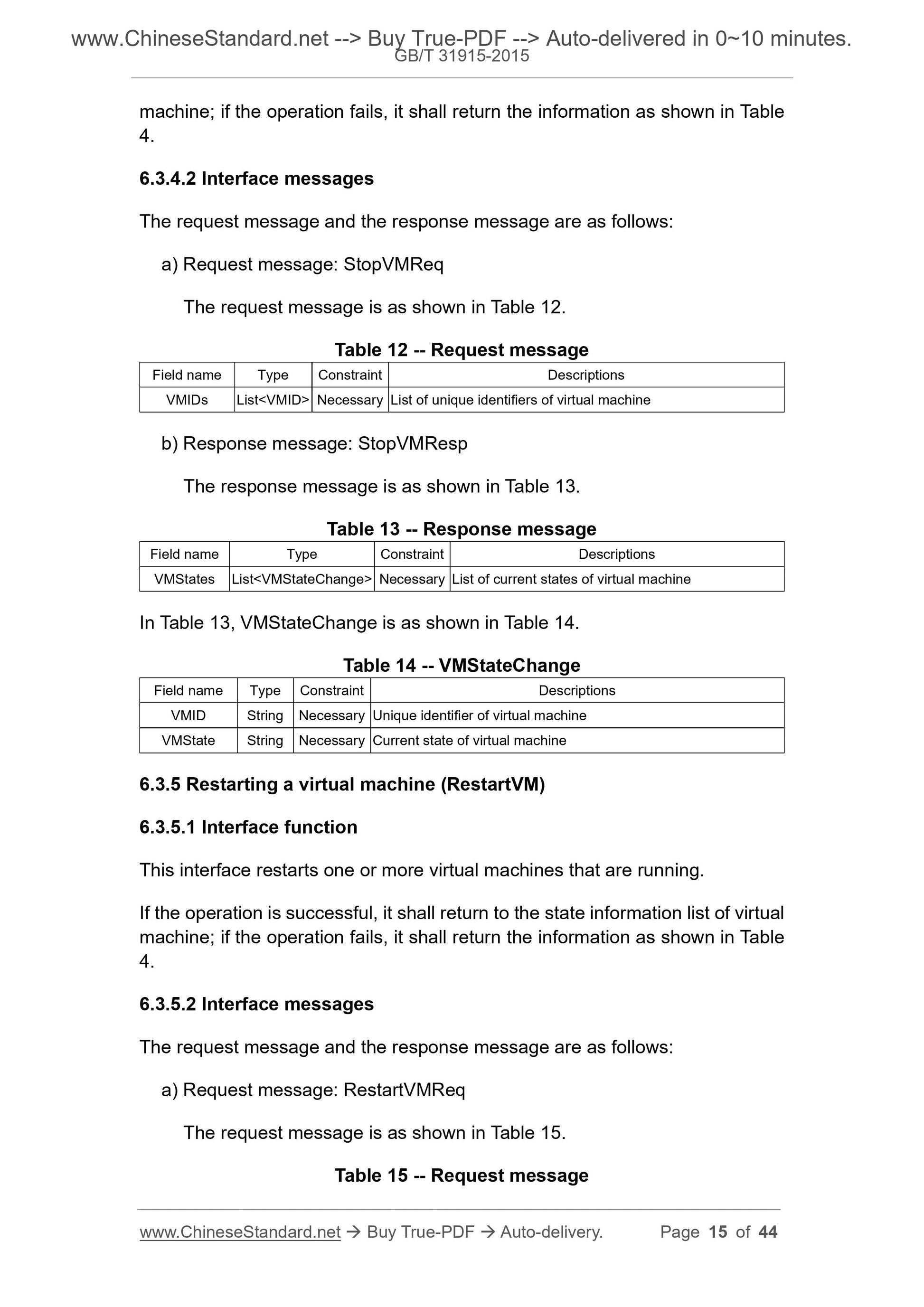
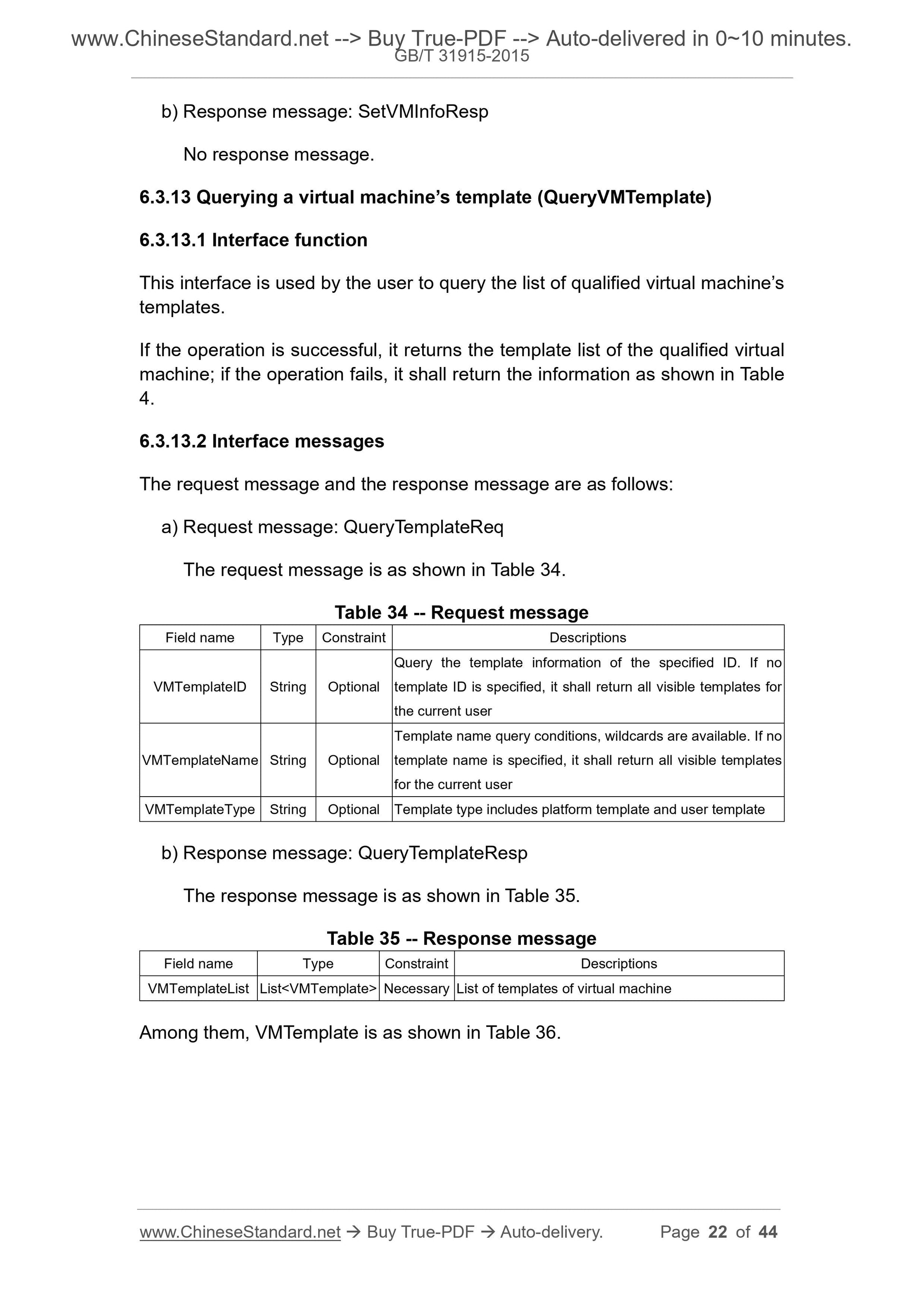
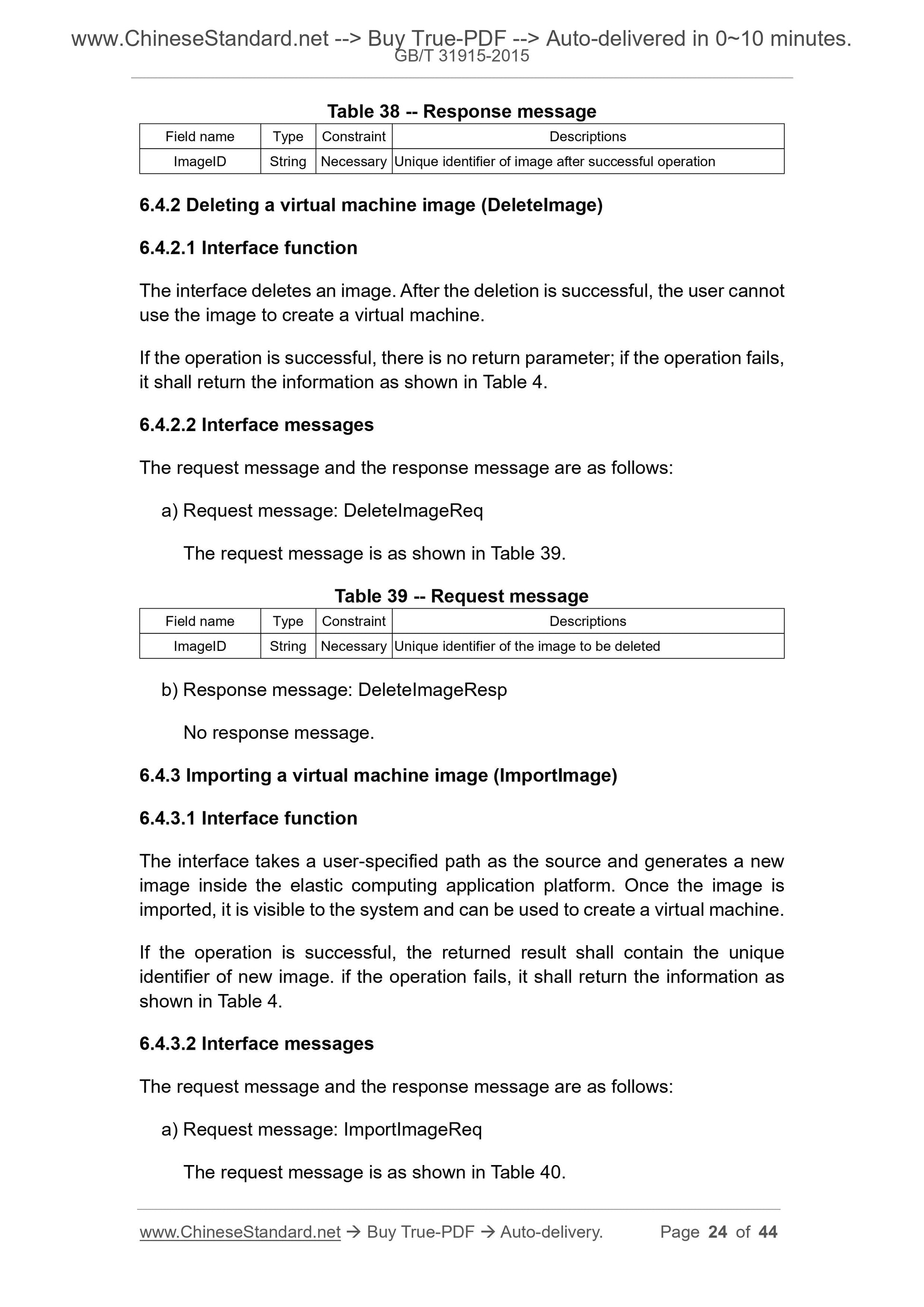
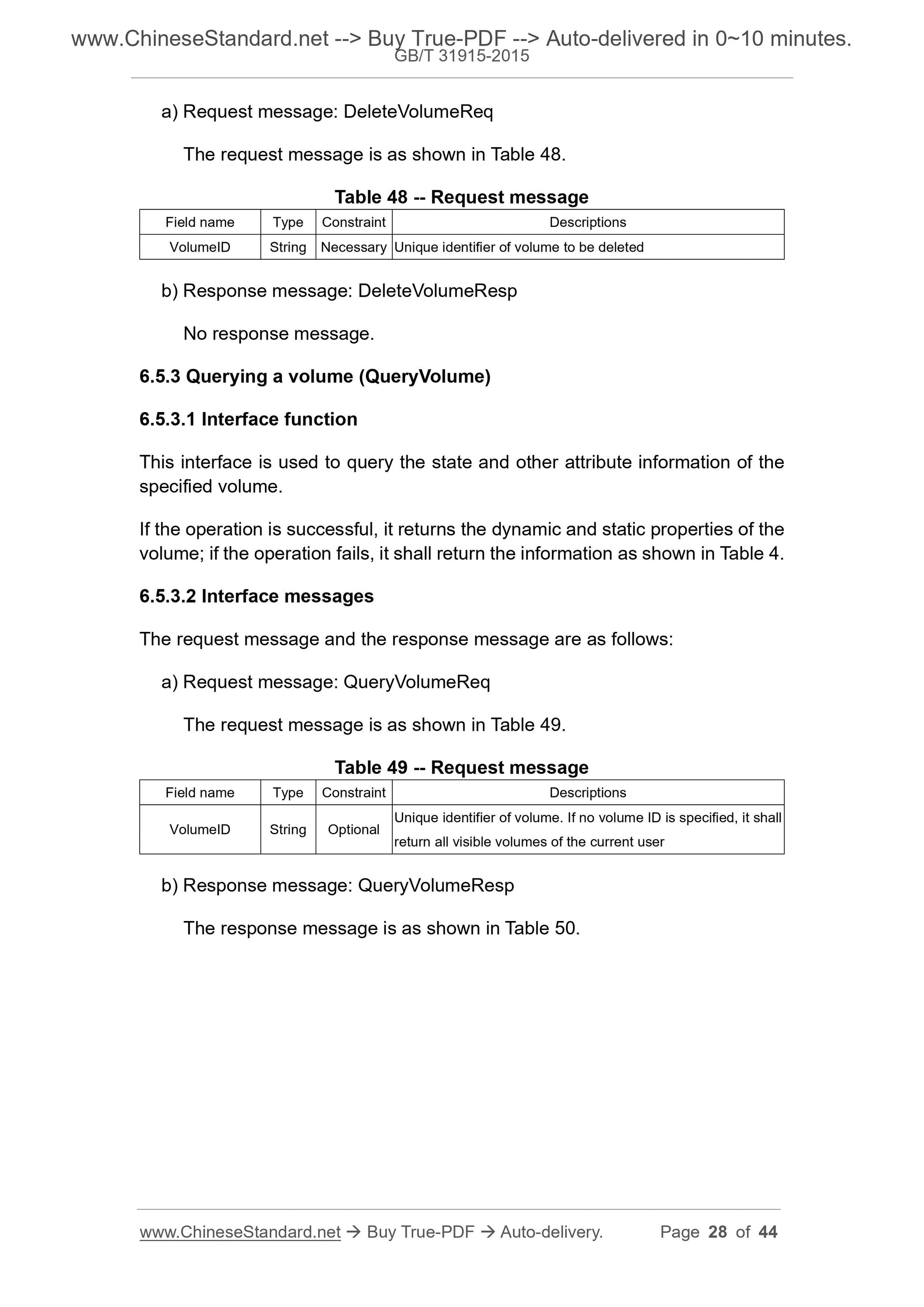
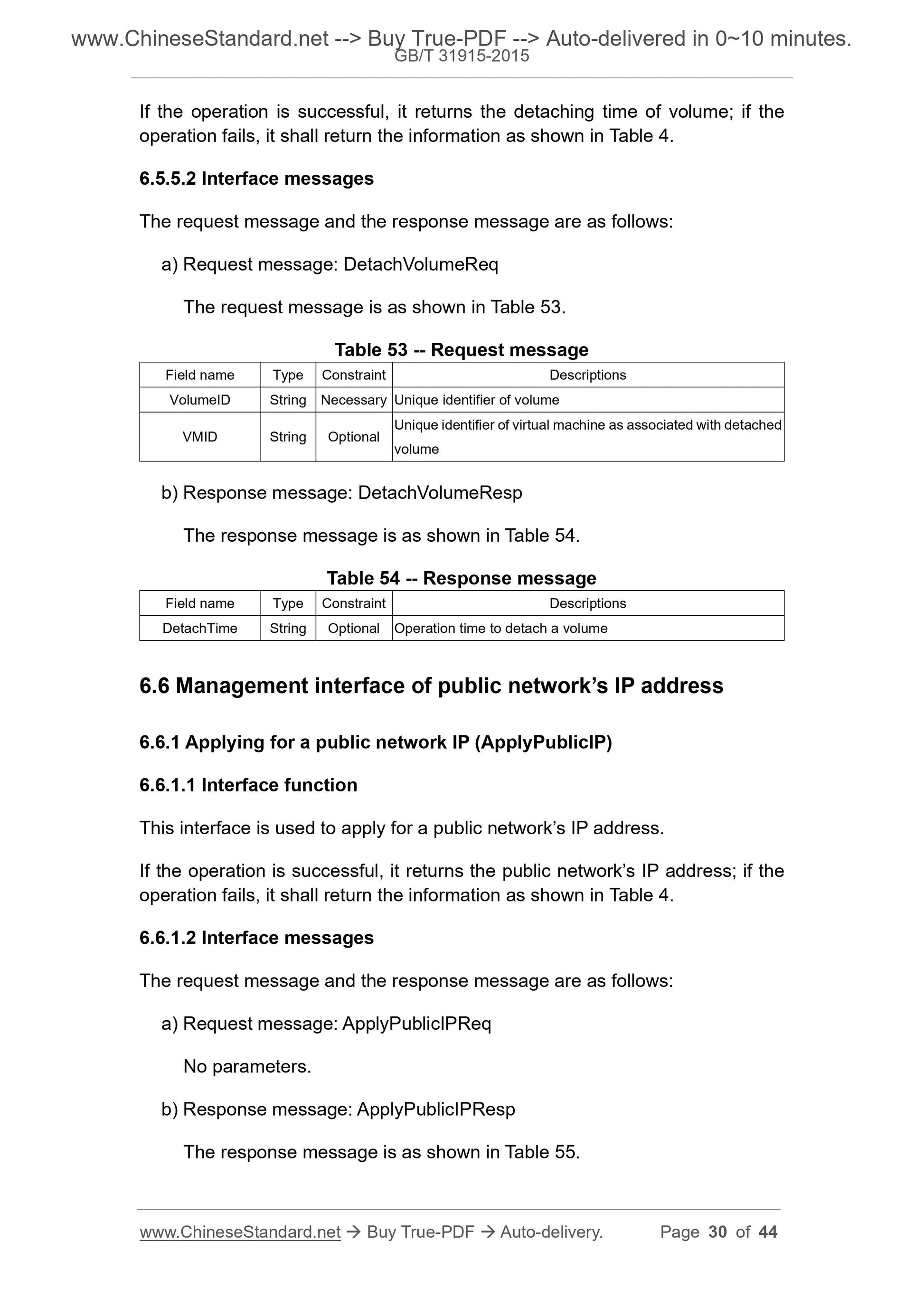
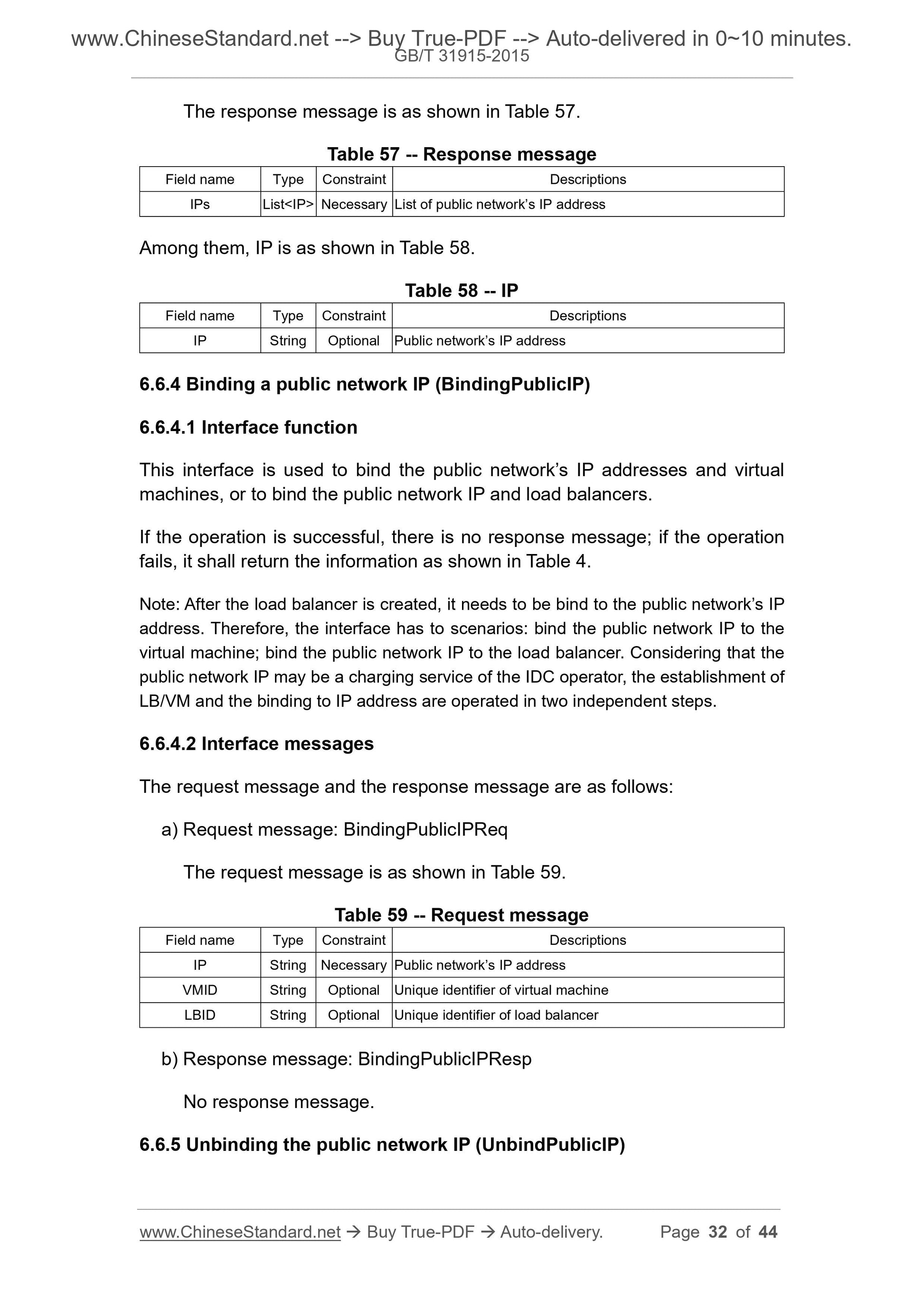
GB/T 31915-2015: Information technology - Elastic computing application interface
Delivery: 9 seconds. Download (and Email) true-PDF + Invoice.Get Quotation: Click GB/T 31915-2015 (Self-service in 1-minute)
Newer / historical versions: GB/T 31915-2015
Preview True-PDF
Scope
This standard gives the elastic computing architecture; specifies the generalrequirements and interface definitions of the elastic computing application
interface.
This standard applies to the design, development, service provision of the
elastic computing application interfaces.
Basic Data
| Standard ID | GB/T 31915-2015 (GB/T31915-2015) |
| Description (Translated English) | Information technology - Elastic computing application interface |
| Sector / Industry | National Standard (Recommended) |
| Classification of Chinese Standard | L79 |
| Classification of International Standard | 35.100.05 |
| Word Count Estimation | 37,392 |
| Date of Issue | 2015-09-11 |
| Date of Implementation | 2016-05-01 |
| Quoted Standard | GB/T 7408-2005; RFC 2616 |
| Regulation (derived from) | National Standard Announcement 2015 No.25 |
| Issuing agency(ies) | General Administration of Quality Supervision, Inspection and Quarantine of the People's Republic of China, Standardization Administration of the People's Republic of China |
| Summary | This Standard specifies the flexible computing architecture, provides flexible computing application interface General requirements and interface definitions. This Standard applies to flexible computing application interface design, development and service delivery. |
Share