1
/
of
12
PayPal, credit cards. Download editable-PDF and invoice in 1 second!
GB/T 20984-2007 English PDF (GB/T20984-2007)
GB/T 20984-2007 English PDF (GB/T20984-2007)
Regular price
$225.00
Regular price
Sale price
$225.00
Unit price
/
per
Shipping calculated at checkout.
Couldn't load pickup availability
GB/T 20984-2007: Information security technology -- Risk assessment specification for information security
Delivery: 9 seconds. Download (and Email) true-PDF + Invoice.Get Quotation: Click GB/T 20984-2007 (Self-service in 1-minute)
Newer / historical versions: GB/T 20984-2007
Preview True-PDF
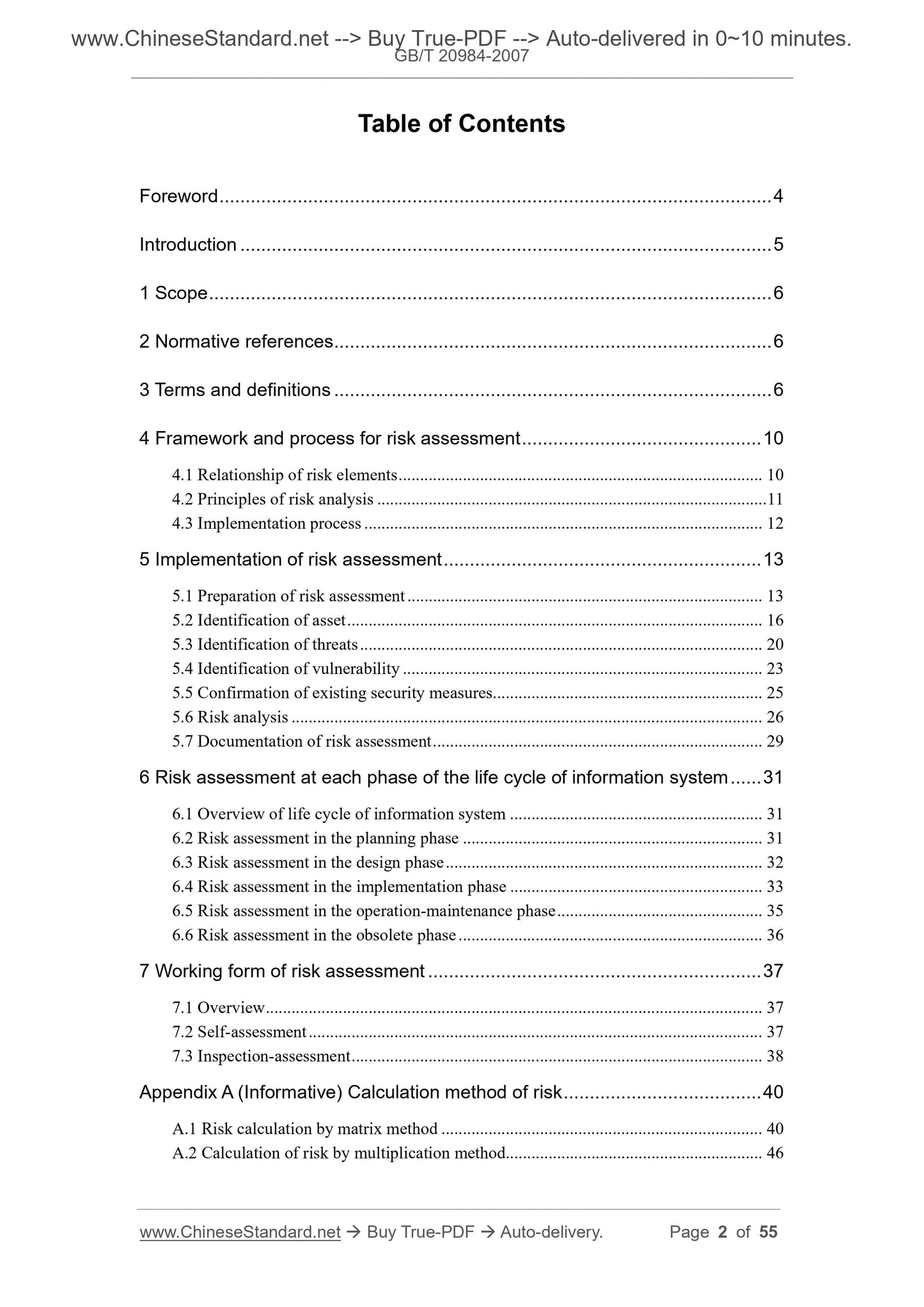
Scope
This standard proposes the basic concepts, element relationships, analysisprinciples, implementation processes, assessment methods of risk assessment,
as well as the implementation key-points and working forms of risk assessment
at different stages of the life cycle of information system.
This standard applies to normalizing the risk assessment work carried out by
the organization.
Basic Data
| Standard ID | GB/T 20984-2007 (GB/T20984-2007) |
| Description (Translated English) | Information security technology -- Risk assessment specification for information security |
| Sector / Industry | National Standard (Recommended) |
| Classification of Chinese Standard | L80 |
| Classification of International Standard | 35.040 |
| Word Count Estimation | 31,398 |
| Date of Issue | 2007-06-14 |
| Date of Implementation | 2007-11-01 |
| Quoted Standard | GB/T 9361; GB 17859-1999; GB/T 18336-2001; GB/T 19716-2005 |
| Regulation (derived from) | GB Notice 2007 No. 6 (Total No. 106) (GB Commission) |
| Issuing agency(ies) | General Administration of Quality Supervision, Inspection and Quarantine of the People's Republic of China, Standardization Administration of the People's Republic of China |
| Summary | This standard specifies the basic concepts of risk assessment, elements of relationship analysis principles, implementation process and assessment methods and risk assessment in the information system life cycle at different stages of the implementation of the key points and forms of work. This standard applies to regulate the organization to carry out a risk assessment. |
Share